Analysts point out that Ethereum uses elliptic curve cryptography in its consensus.
Steve Tippeconnic, a quantum developer, believes that “Ethereum has a more complex structure.”
The possibility of quantum computing breaking into current cryptographic systems continues to generate discussions among analysts, researchers and users.
In that sense, the bitcoiner developer known in X as LLFOURN and member of the Frostsnap hardware wallet team, sumo to a discussion in X.
His position is blunt:
Ethereum has much bigger problems with quantum than Bitcoin.
LLFOURN, bitcoiner developer.
The statement refers to structural differences between both networks and how cryptography supports essential functions such as consensus security, signature validation and safekeeping of funds.
Along the same lines, Steve Tippeconnic, a quantum developer at IBM, told CriptoNoticias that Ethereum faces a wider attack surface:
At a macro level, Ethereum’s architecture is more complex, with smart contracts, multiple signature schemes, and a larger cryptographic footprint. That implies it could have more components to upgrade than Bitcoin in a post-quantum era.
Steve Tippeconnic.
Reasons why Ethereum would be more vulnerable than Bitcoin to quantum
LLFOURN supported three central arguments:
First of all, he noted that Ethereum’s consensus mechanism, based on Proof of Stake (PoS), depends on ECDLP (discrete logarithm on elliptic curves), a form of cryptography vulnerable to quantum computing and algorithm Shor.
In the developer’s words:
The Ethereum consensus depends on ECDLP and therefore the consensus itself is broken by quantum computers.
LLFOURN, bitcoiner developer.
Bitcoin also uses elliptic curve algorithms, specifically the one known as ECDSA (digital signature algorithm based on elliptic curves).
However, the difference between both networks lies in where these vulnerable cryptographies (ECDLP and ECDSA) operate in each network. In Bitcoin, the ECDSA scheme is only used to sign transactions, but does not participate in the consensus mechanism like yes in Ethereum.
Therefore, in Bitcoin, an eventual quantum break would allow funds whose public key is already known to be compromised (reused addresses), although it would not affect the validation of blocks or the operation of the consensus.
The consensus mechanism used in Bitcoin, proof of work (PoW), depends on the SHA-256 algorithm, which is more quantum resistant (it would only be vulnerable to the much slower attack of Grover). Additionally, automatically adjusting mining difficulty mitigates what a quantum attacker could do.
This scenario would allow the network created by Satoshi Nakamoto to migrate towards a quantum-resistant scheme through a soft fork (changing only the signature scheme and address formats), without the need to rewrite your consensus structure.


Impact on Ethereum consensus: the potential quantum risk
If a quantum computer managed to break the cryptographic signatures that underpin the Ethereum consensus, the impact would reach the heart of the protocol.
An attacker capable of generating signatures at the consensus level without knowing the private keys could impersonate validators, cast false votes and disrupt the process by which the network defines which blocks are valid.
By being able to sign on behalf of real validators, the attacker would have the ability to influence consensus voting, introduce fraudulent blocks, or even reorganize the chain if it manages to forge enough signatures.
The risk does not come from the loss of funds, but from the possibility of directly manipulating the machinery that keeps the chain coherent.
In that sense, Tippeconnic, who demonstrated that the risk in Bitcoin against quantum is realhighlighted the fragility of the Ethereum consensus, although his view offers more caution:
Both ecosystems face challenges and both must prepare for a quantum future. We still don’t know what the best transition path will be.
Steve Tippeconnic.
The Ethereum virtual machine (EVM), another weak point for the network
The second point that developer LLFOURN points out is the Ethereum virtual machine (EVM): “Ethereum never incorporated (in the EVM) a standard ECDSA signature verification,” he stated.
Instead use ecrecovera function that allows recovering addresses from signatures, but that makes it difficult to migrate to quantum-resistant schemesaccording to LLFOURN.
This bitcoiner developer, similar to what Tippeconnic said, considers that Ethereum has a more complex field to defend against a quantum attack:
It cannot be a direct replacement for a post-quantum signature scheme. Every smart contract that uses ecrecover must be rewritten.
LLFOURN, bitcoiner developer.
That implies that thousands of contracts deployed should be modified manuallysomething that could be slow and complex.
Ethereum would have more public transaction keys exposed
The third point addresses the exposure of public keys. LLFOURN, without offering specific data, stressed:
The majority of ether on Ethereum is in addresses with revealed public keys, so this is a strong point in favor of Bitcoin over Ethereum.
LLFOURN, bitcoiner developer.
When a public key is already exposed, a quantum computer could derive the private key and steal the associated funds.
According to that analysis, Bitcoin has a smaller portion of coins under addresses that only reveal the public key at the time of being spent, which reduces the attack surface.
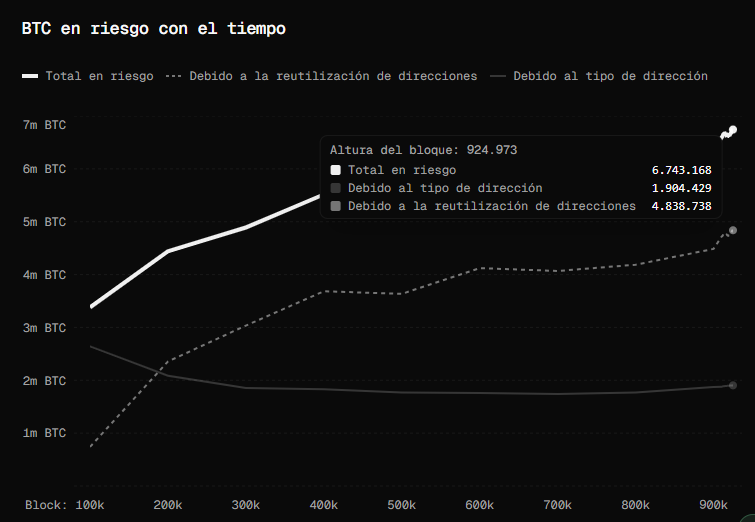
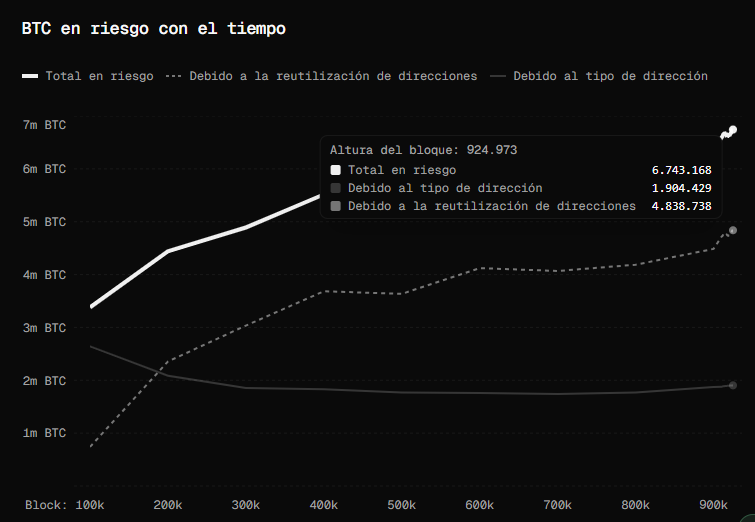
Even so, and as CriptoNoticias already reported, there are almost 7,000,000 BTC in exchange holdings at risk of being stolen by a quantum attacker due to address reuse.
Finally, LLFOURN closed his arguments by indicating that even in a scenario where there was a “slow quantum” phase (a period in which quantum computers are dangerous, but not yet fully powerful) Ethereum would not be well positioned either.





Leave a Reply