On April 1, 2026, like a bad April Fool’s joke, the largest decentralized perpetual futures exchange Solana was tricked into a hack of approximately $285 million in just 12 minutes. It was not a mistake in the code. It was not a exploit smart contract. It was pure social engineering, a hoax hatched for about half a year.
Drift Protocol, the victim of the hack, confirmed this in its own statement: the attackers infiltrated conferences, held face-to-face meetings, gained trust and obtained Security Council signatories (multisig) pre-signed transactions that seemed routine. Those signatures, thanks to durable nonces in Solana (a feature that allows you to create a special persistent authorization account, with which a transaction can be signed in advance and executed long into the future), were executed weeks later and allowed for a full administrative takeover.
User funds, vaults loans and the Insurance Fund were drained. Then, more than 230 million in USDC were bridged to Ethereum via Circle’s Cross-Chain Transfer Protocol in more than 100 atomic transactions. It took Circle over six hours to react and freeze something. By then, the damage had already been done: the second largest hack in the history of Solana, after the attack on Wormhole in 2022.
But the real scandal is not just the amount. This is what it reveals about the current state of security in the cryptocurrency industry: The human is, now more than ever, the weakest link.
No matter how many audits are done on smart contracts; no matter how many signatories are included in the contracts multisig; No matter how many temporary blocks are added to transactions, in practice, The last step is always a human being. And, it seems, the North Koreans, the usual suspects in these attacks, know this better than anyone.
The Lazarus group (also known as UNC4736, AppleJeus, Golden Chollima) has been perfecting this tactic for years. Not only in Drift. According to recent forensic reports, developers linked to Pyongyang infiltrated open source projects such as SushiSwap, Harmony and even Shiba Inu for years. They used fake GitHub identities, clean profiles, and slow, consistent contributions to gain access to the codebase. They didn’t need magical exploits. Just patience and human trust.
At Drift it was even more sophisticated: six months of preparation, face-to-face meetings at conferences, own deposits to build credibility, and the creation of customer accounts. nonce lasting since March 23. Everything culminated on April 1 with an attack in minutes. Elliptic and TRM Labs they attribute it with high confidence to actors sponsored by the North Korean state because they repeat patterns identified in previous attacks.
Although these types of attacks were already possible in the past, artificial intelligence and deepfakes they elevate them to systemic risk. Today anyone can buy tools on the darknet as ProKYC or kits deepfakes in real time that combine face-swap with voice cloning. Just 30-90 seconds of public audio from a person is enough to generate an indistinguishable voice. A photo and a 10-second video are enough to create a synthetic identity that passes video KYC verifications at exchanges and banks. The fabric of reality is compromised and, in the middle of the tangle, we are all in danger.


It is no longer about crude phishing with poorly written emails. Now it’s your “boss” calling you on Zoom with a perfect voice and face asking you to approve an urgent but routine transaction. Or your “friend” from the trading team sending you a link to a meeting where they ask you to pre-sign something to streamline governance. Who detects that? The retail user who manages their wallet on their cell phone? A signatory of multisig of company or DeFi platform in a protocol of hundreds of millions? Anyone can fall.
What will happen when this same vector targets the large traditional players that are entering the industry via real asset (RWA) tokenization? Let’s imagine the scenario: JP Morgan tokenizing money market funds on Ethereum. Credit Suisse issuing institutional stablecoins or tokenized deposits. A sovereign wealth fund or digital central bank experimenting with CBDC in DeFi. Is Lazarus going to respect them?
In 2025 alone, North Korea stole more than $2 billion in crypto according to Chainalysisan increase of 50% compared to 2024. Money that finances missiles, weapons and the regime’s nuclear program.
When the hack is not of a Solana DEX but of an infrastructure that touches Wall Street, the response will not be impunity and indignant tweets. It will be a national security incident. And the discourse will change from DeFi failure to an act of war.
The underlying problem is the same in all cases: the digital and automated world continues to depend on human decisions. AI accelerates everything: from writing an email or generating a business plan to social engineering; everything is cheaper, more scalable and almost impossible to detect in real time. And the sophistication of this type of technology only continues to advance.
We have already seen such terrifying cases of live phishing during Zoom calls, such as it happened with the co-founder from the Polygon network, Sandeep Naiwal, or with the co-founder of Manta NetworkKenny Li. In both cases, the goal was to convince the victim to install a file that turned out to be malware that would steal their cryptocurrency. In other cases, North Korean agents and organized crime groups have used deepfakes to impersonate remote job applicants, successfully accessing internal systems in multiple sectors.
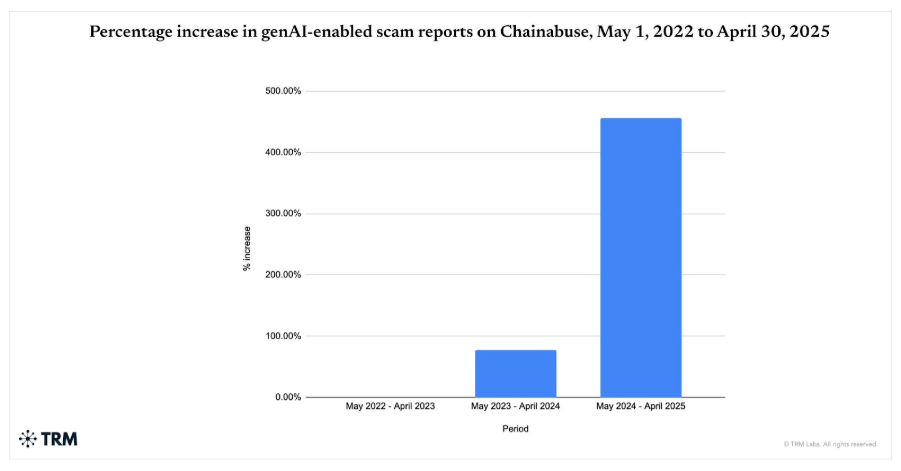
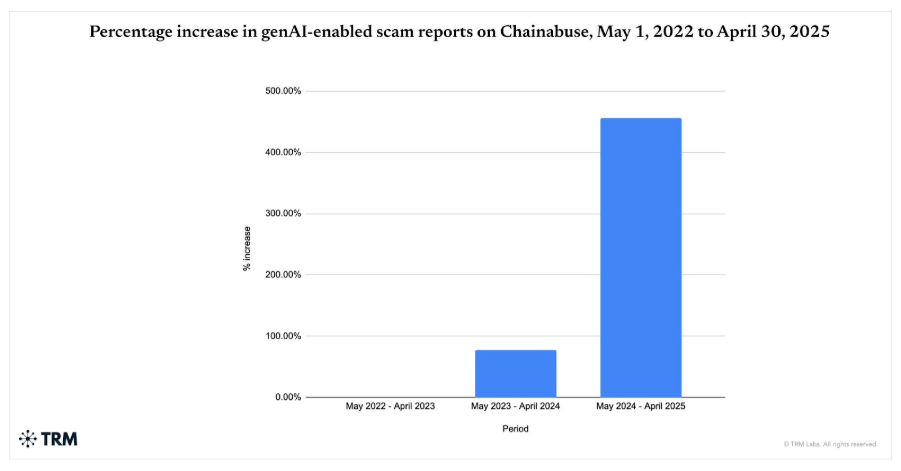
According to Chainabuse dataTRM Labs’ fraud reporting tool, scams facilitated with generative artificial intelligence between May 2024 and April 2025 increased 456%, compared to the same period between 2023 and 2024.
There is no technological silver bullet. Offline verification, such as real phone calls through verified back channels or physical meetings for critical signatures, is expensive and time-consuming, yet has proven insufficient to prevent scams. Although education can help mitigate the danger, studies have shown that it is not a barrier against scams and hacks, since the victims are often adults with higher education – even successful professionals – and it cuts across genders, ages and social classes.
Major identity verification companies have evolved to multi-layer systems that combine advanced biometrics, real-time analysis and on-chain intelligence.
Cryptocurrency KYC company Sumsub offers real-time video deepfake detection tools (not just static images) with 99.98% accuracy. It launched a free and open machine learning model called “For Fake’s Sake” that detects deepfakes and synthetic frauds. In 2025, it integrated its Crypto Monitoring solution with TRM Labs to combine identity verification with on-chain risk in a single dashboard. This allows transactions to be blocked to high-risk wallets before they are executed.
Reality Defender, recognized by Gartner as the leader in deepfake detection, offers a multimodal API that analyzes voice, image and text in real time and is already integrated into video calling and exchange KYC platforms.
For the common user, however, The first and most powerful line of defense remains distrust and verification. Never trust a video, voice or video call without independent verification: if someone asks you to send cryptocurrency, call a number you already know, not the one they give you at the time. Establish “safe words” with family, friends or colleagues to confirm identities in emergencies. In a suspicious call, ask for something unpredictable — turning your head to the side, holding a random object, or answering an unrehearsed personal question — because real-time deepfakes still fail at synchronicity and unexpected angles.
Drift was a warning, a reminder that in cryptocurrencies the biggest vulnerability is not in the code. It’s in the mirror. It’s us. And as long as we continue to trust that the other side of the transaction is who they say they are, Lazarus—and anyone with darknet access and a Midjourney subscription—will continue to have an avenue into your cryptocurrencies.
