Old addresses (P2PK) and Taproot addresses (P2TR) have 100% of their public keys exposed.
Migrating the funds to secure addresses would take approximately 157 days of continuous processing.
Bitcoin currently has 16,039,132 public keys exposed on the chain to potential attacks with quantum computers, according to data from an on-chain analysis platform developed by the bitcoiner programmer known in X as Wicked.
This amount of public keys corresponds to about 6,920,868 BTC (34.58% of the network’s total supply), equivalent to almost USD 500,000 million.
An exposed public key is one that became visible on the blockchain after its owner carried out a transaction or by the design of the type of address he uses.
That is relevant to the post-quantum debate because the algorithm of Shorexecutable on a sufficiently powerful quantum computer, could in theory use that public key to derive the corresponding private key and access the funds. Without a visible public key, such an attack is not possible.


Additionally, this exposure is important even today, before there is quantum hardware capable of taking advantage of it. As the ANSSI and other security agencies warn, there is a practice known as “harvest now, decrypt later” (harvest now, decipher later).
With this technique, malicious actors can Capture and store those exposed public keys today to try to derive the corresponding private keys in the future, when they have a sufficiently powerful quantum computer. That means funds at addresses with exposed keys could be being harvested now, even though the attack cannot be executed yet.
The most exposed types of management
He breakdown by type of address shows significant differences in the level of exposure. The P2PK (Public Key Payment) addresses, corresponding to the Satoshi era and the oldest on the network, They have 100% of their 1,716,320 BTC exposed.
Next, P2TR (Taproot Payment in Root) addresses, the Taproot format introduced in 2021, They also have 100% of their 205,581 BTC exposedsince by design they publish the public key directly on the chain.
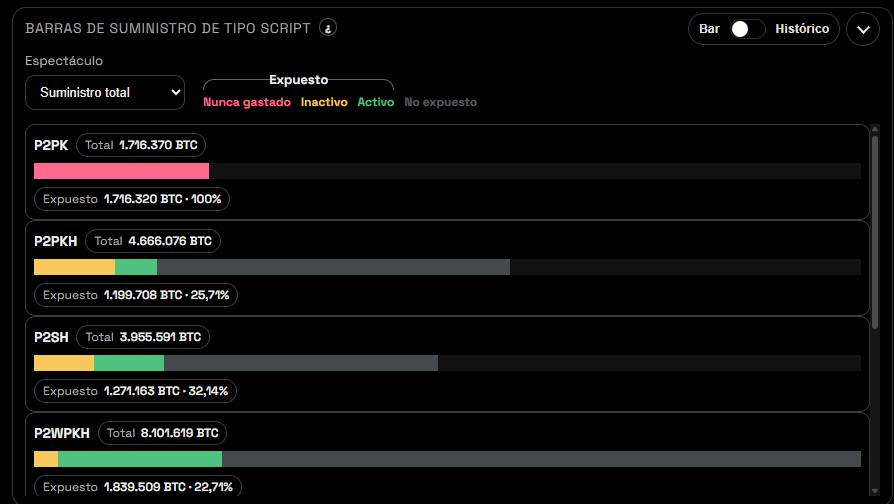
In other formats, the exposure is partial: P2WSH (Payment to Witness Script Hash) shows 50.46% of its funds exposed; P2SH (Payment to Script Hash) 32.14%; P2PKH (Payment to Public Key Hash) 25.71%; and P2WPKH (Payment to Witness Public Key Hash) 22.71%.
Just because a key is exposed doesn’t mean funds are at risk today. The quantum attack that could take advantage of that exposure requires hardware that doesn’t yet exist.
Finally, what Wicked’s data does illustrate is the scale of the migration challenge: moving all those funds to addresses with unexposed keys would take approximately 157 days of continuous network processingas estimated by the tool. This data coincides with previous Circle estimates reported by CriptoNoticias, which calculated a similar time frame to migrate all vulnerable UTXOs (unspent transaction outputs) from Bitcoin.
