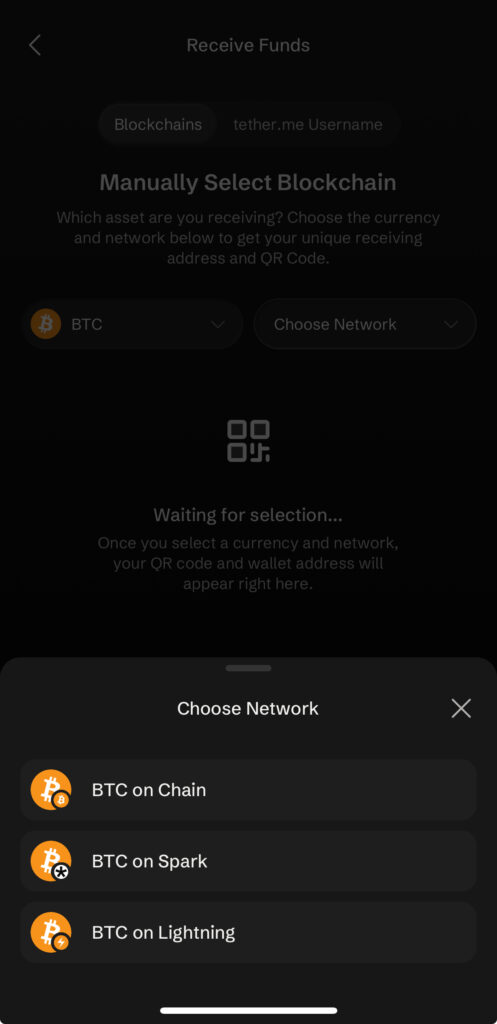
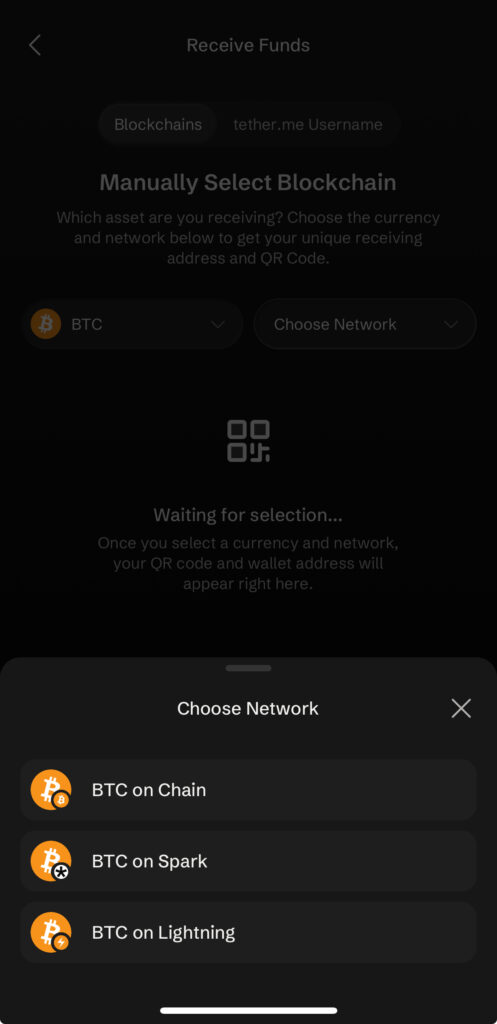
It integrates BTC on-chain, Lightning and Spark, ideal for different types of use.
It allows you to send USDT without paying fees with native tokens from networks such as Ethereum or Arbitrum.
This April 14, Tether announced the launch of Tether Wallet, its own official self-custody application for bitcoin (BTC), USDT, USDA, XAU₮ (the gold tokenized version of Tether), and in this article we thoroughly review how it works.
Tether Wallet: mobile-only app
In principle, Tether Wallet, as reported by CriptoNoticias, is an application available exclusively for mobile devices on iOS and Android, which limits its use to these environments and leaves out those who operate from computers or seek broader integrations with desktops or hardware wallets.
Next, in practice, downloading and installing are as simple as any other mobile application (Apple Store in this case).
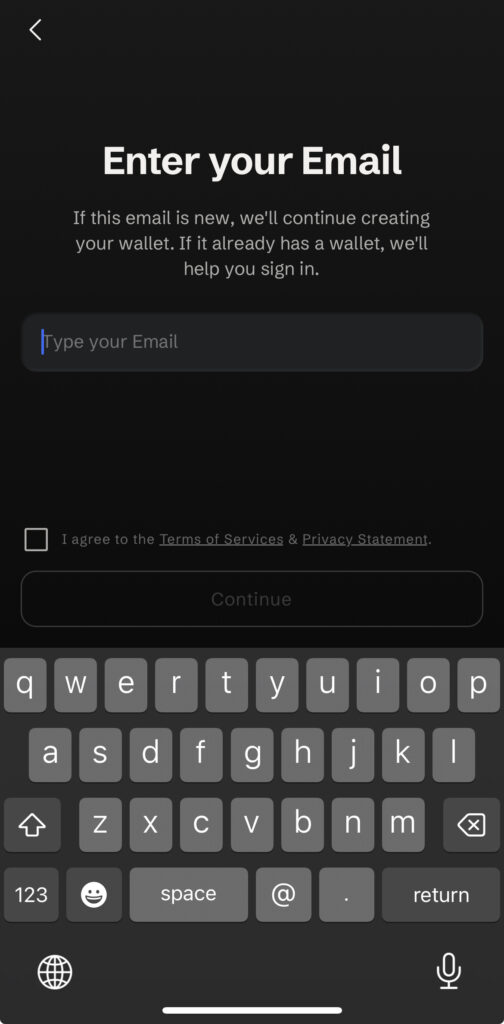
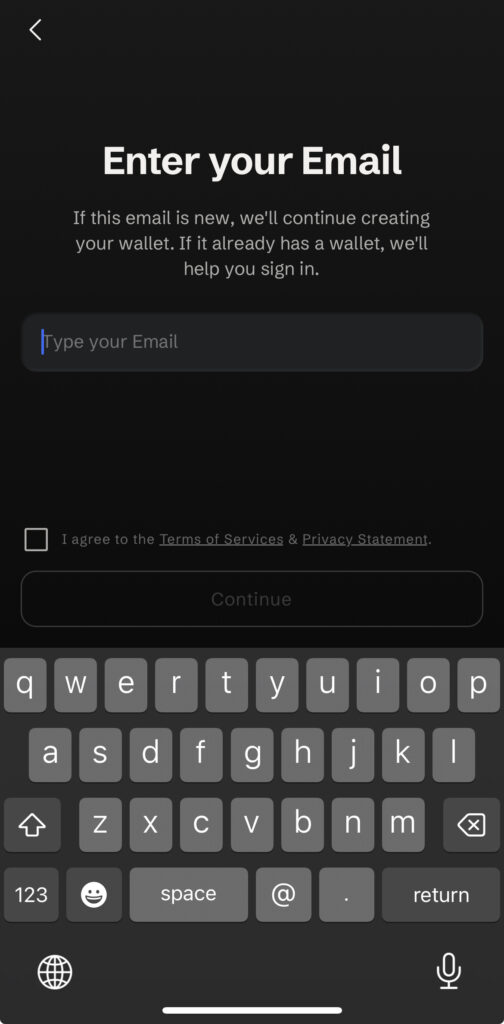
However, as seen in the following screenshot, The registration process requires an email to create or access the wallet, which introduces a user identification vector: although self-custody is maintained at the key level, the link with an email reduces the level of anonymity by associating on-chain activity with a potentially traceable identity.
The registration email, which cannot be skipped, is used to log into Tether Wallet if the user logs out of the app.
The app, when creating an account, requires the selection of a username in the format ‘@tether.me’, which works as a payment alias and replaces the typical long addresses with something much easier to remember and share. This greatly improves the user experience and reduces errors when sending funds, although in exchange it introduces a certain dependency on Tether’s infrastructure for these names to work correctly.
In addition, there is a practical limitation: if use grows, the simpler names will become more common, which can push new users to choose rarer or less intuitive combinations to find one available.
A negative aspect is the requirement to include yes or yes a number in the name that users choose in the format ‘@tether.me’.
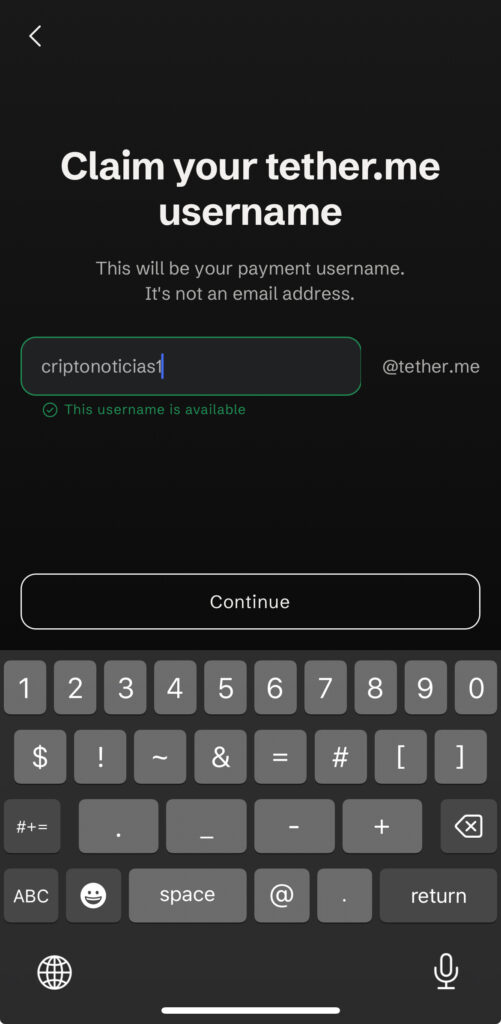
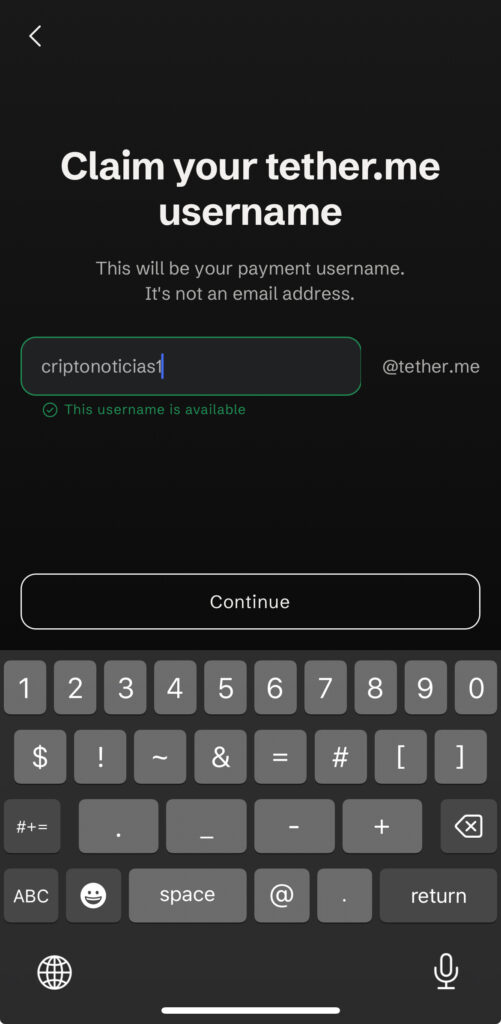
The mechanism of giving a name to accounts in the ‘@tether.me’ format of Tether Wallet already exists in other wallets in the bitcoiner ecosystem. For example, in Wallet of Satoshi it is ‘user@walletofsatoshi.com’.
Tether Wallet and Bitcoin: unique address format
In operational terms, sending and receiving funds behaves like any standard wallet and not like a “bitcoin only” wallet. This is because, when creating the wallet, cannot select address format that is intended to be used, but Tether Wallet automatically generates a native SegWit type address (Bech32 format, specifically P2WPKH).
While that format is the most common currently, from the perspective of a bitcoiner who values individual sovereignty and technical control over their keys, this limitation represents a disadvantage.
Not allowing the user to choose between Native SegWit, Taproot or other formats implies a loss of autonomy when deciding how to derive and use their addresses. Taproot (bc1p), for example, offers improvements in privacy, fee efficiency and preparation for advanced uses such as multi-signature (multisig) or Lightning Network (LN).
Forcing a single bypass option, although functional, conveys a philosophy more oriented toward massive simplicity than maximum user sovereignty, reminiscent more of generalist wallets than of tools designed for those seeking the greatest possible control over their interaction with the Bitcoin protocol.
Tether Wallet does not integrate the CoinControl techniquea practice to manage UXTOs (unspent transaction outputs) and manually choose which UTXOs to use in a transaction, avoiding, for example, mixing certain funds for privacy.
Tether Wallet reuses Bitcoin addresses
On the other hand, Tether Wallet Permanently reuse the same on-chain BTC address and does not allow generating new addresses. Once the wallet is created, it always displays and uses that single ‘bc1q… address to receive funds at the base layer.
This practice negatively affects privacy, since always reusing the same address makes it extremely easy to track all incoming and outgoing transactions by external observers.
Additionally, from a quantum perspective, the potential risk in the future increases. By reusing the same address, the public key is continuously exposed, expanding the window of vulnerability to the theoretical arrival of a quantum attack.
Move bitcoin in Tether Wallet: a massively used wallet
To move bitcoin, the Tether wallet allows you to operate both on the main network (on-chain) and on the second layer (L2) Lightning and Spark networks, which positively favors different uses of the asset within the same self-custody environment.
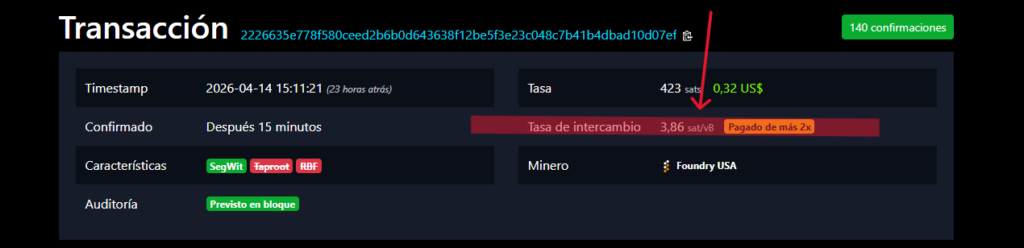
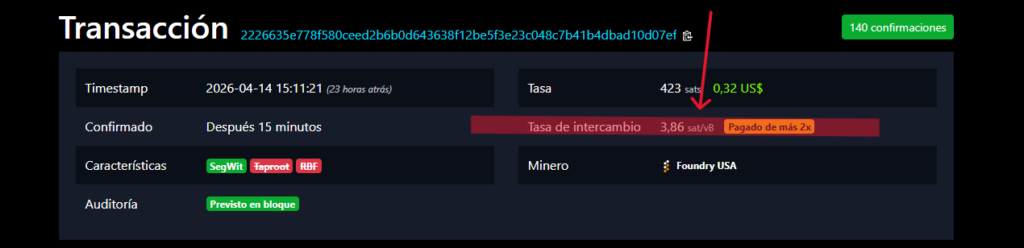
In the on-chain layer, the experience showed certain practical limitations. in a transaction The Tether wallet applied a rate of 3.86 sat/vB (USD 0.32), while the block accepted transactions from 1.20 sat/vBwhich implies higher costs than necessary when the network was not congested. It was also not possible to modify the commission rate when submitting the transaction.
Send and receive USDT in Tether Wallet
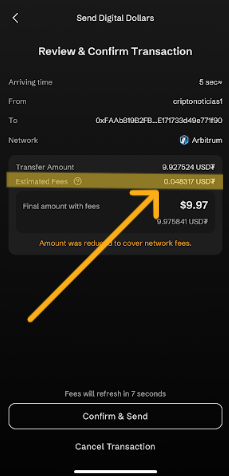
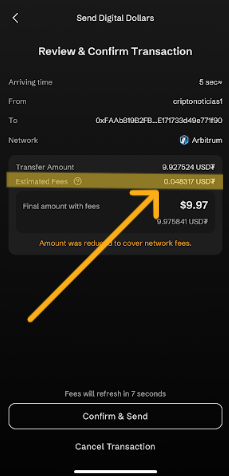
Regarding USDT transfers, the Tether app has a specific advantage here. To move your stablecoin, Tether Wallet allows the Ethereum, Arbitrum, Polygon and Plasma networks to do so. allowing payment of commissions directly in USDT.
That advantage eliminates the need to hold native tokens like ether (ETH) or Arbitrum ARB to cover network fees, making the user experience simpler and faster.
However, this versatility coexists with a structural characteristic of USDT itself: the ability to freeze funds by Tether. According to their own policiesTether can block access to USDT in any wallet and also access to the Tether Wallet interface if you consider it necessary.
However, it is important to highlight that, although the company can freeze the USDT, it does not have the ability to block the BTC that the user keeps in the same wallet, since these remain under self-custody and are technically uncontrollable by third parties.
Self-custody in Tether Wallet
Regarding self-custody, Tether Wallet uses a 12-word recovery seed generated locally on the device, which aligns with the ecosystem standard.
However, it introduces a mechanism optional encrypted backup in the cloud (iCloud on iOS or Google Drive on Android), where the wallet data is stored on Tether servers in encrypted form, while the decryption key remains in the user’s personal account. Tether recommends using this option.
Although the model separates both parts, From a bitcoiner perspective this implies trusting third parties (cloud providers and Tether itself), which can be considered a commitment to the ideal of sovereign self-custody based exclusively on storage offline.
Conclusion
Overall, Tether Wallet is presented as a practical and accessible solution that correctly fulfills the basic functions, integrating BTC and USDT with multi-network support into a single interface, although with limitations in autonomy and privacy.
Its main value lies in the simplicity of use, especially in the management of commissions and addresses, although it introduces trade-offs in terms of privacy and dependence on centralized infrastructure that must be considered according to the user profile.
