The bot deployed $1.14 million in capital to extract between $5 and $15 from the trade.
Buterin proposed encrypted mempools in March as a solution to these types of attacks.
A wallet associated with Vitalik Buterin, co-founder of Ethereum, was the victim of a type of on-chain attack called a MEV (maximum extractable value) sandwich, executed by the bot operating under the name ‘jaredfromsubway.eth’. The attack was carried out on block 24993038, processed on April 30, according to data from the etherscan explorer.
A sandwich attack occurs when a bot detects a large transaction pending confirmation in the mempool. This place two transactions of your own around the victim: one before and one after. The first operation buys the token that the user wants to sell, pushing its price up; the second sells it immediately.
As a result, the user, in this case Vitalik, is caught in the middle and receives less money than he would have gotten without the interference.
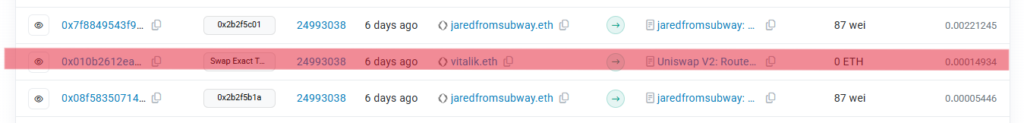
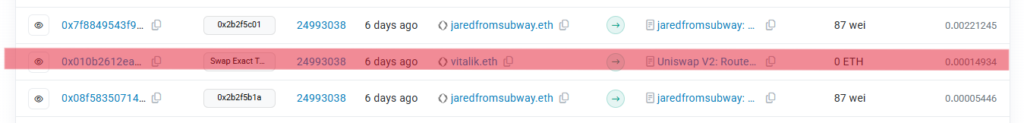
The wallet associated with Buterin was selling 751,644 XDB tokens (digitalbits) on Uniswap V2, a decentralized exchange protocol on Ethereum, for a value of just $110.
To intercept that operation, the bot deployed approximately $1.14 million in capital (the volume needed to move the price of the token in a low-liquidity pool) and extracted between USD 5 and 15 difference.
According to the analyst and researcher known in X as Uttam, liquid buterin periodically received tokens as an airdrop and allocates the funds to charitable donations, so, if so, the sandwich attack not only affected the co-founder of Ethereum but the final destination of those funds.
The co-founder of Ethereum, with proposals but no solution
At the beginning of last March, Vitalik himself had published his ideas to stop this type of attacks. Among the solutions he proposed is the encrypted mempool. It is a mechanism by which Transactions would travel encrypted until they are included in a blockpreventing any bot from detecting and intercepting them before being confirmed.
He also noted improvements to the network layer so that transactions do not travel exposed between the user and the block, reducing the window in which a hostile actor can see them and act.
However, none of these solutions are implemented on Ethereum and, meanwhile, bots like jaredfromsubway.eth continue to operate on the public mempool, regardless of victims.
