Charlie Lee, creator of Litecoin, contributed the 850 LTC paid as a reward to the March attacker.
In April, Litecoin underwent a reorganization of 13 network blocks.
David Burkett, lead developer of Litecoin Core and architect of MWEB (Litecoin’s privacy layer activated in 2022), published the postmortem statement on the Litecoin Foundation website following the two insecurity incidents related to MWEB.
The document shared today, April 28, confirmed that the first exploit March was lossless content for Litecoin users and added a previously unreported fact: Charlie Lee, creator of Litecoin, personally bought the 850 LTC paid as a reward to the attacker to cooperate in the return of the funds.
In this first incident, according to postmortema bug in MWEB’s validation function allowed an attacker to submit false metadata when connecting a block to the chain.
In practical terms, an entry of just 1.2 LTC (almost $66) could be passed off as a much larger amount and authorize an inflated withdrawal. An attacker took advantage of that failure to extract 85,034 LTC (almost USD 4,700,000) of the MWEB layer in a single block, Burkett’s report mentions.
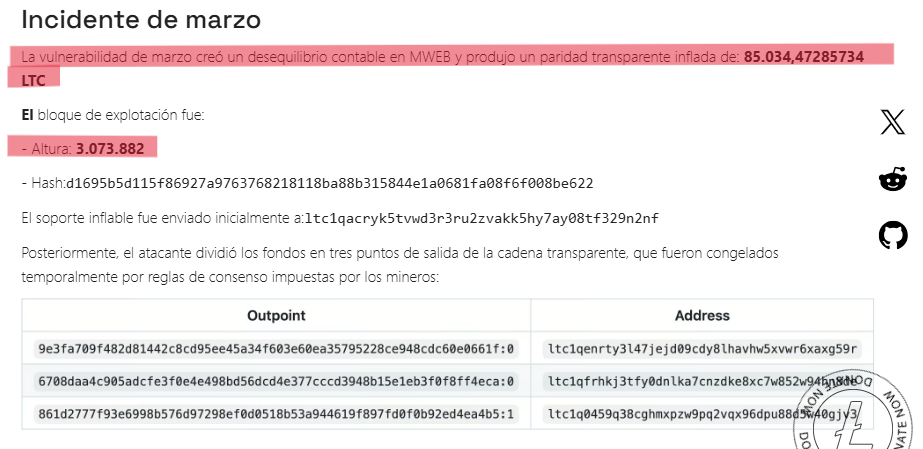
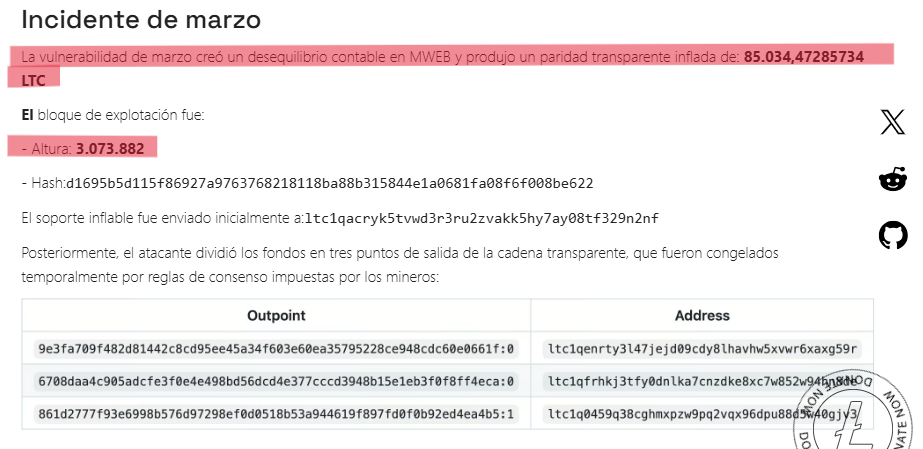
Burkett explains that Litecoin developers detected the vulnerability internally and a scan of the chain confirmed that it had already been exploited. The inflated funds, however, were still intact in three addresses of Litecoin’s public layer, where any transaction is visible on the chain (each Litecoin block can contain an additional “MWEB body” with private transactions).
In coordination with the main mining pools, Those exits were frozen by consensus rulespreventing the attacker from moving them, the Litecoin Core developer argued.
According to Burkett, the team contacted the attacker, who agreed to return the funds in exchange for a reward of 850 LTC. Charlie Lee contributed those 850 LTC to cover the reward, which was added to the amount recovered and re-entered into MWEB. The resulting output was frozen to restore the layer’s accounting balance without those funds being able to circulate again.
According to the postmortem, no Litecoin users lost funds in this incident.


The April incident: reorganization of 13 blocks and losses in third parties
The second incident, reported by CriptoNoticias on April 25, began with a new actor attempting to use the same vulnerability compromised in March. This time, the updated nodes rejected the malicious block, but that rejection exposed an issue that the patch had not addressed.
The mutated data in the MWEB block caused those nodes to become blocked and could not continue operating normally. The non-updated nodes, on the other hand, continued to extend the invalid chain.
To ensure that chain gained traction, The attackers simultaneously launched a denial of service attack (DDoS, a flood of requests designed to saturate and disconnect systems), against the main mining pools that already had the patch.
The combination of blocked upgraded nodes and attacked pools allowed the invalid chain grew to 13 blocksequivalent to approximately 32 minutes of transaction history.


Several cross-chain exchanges processed transactions on that invalid chain before the automatic reorganization that the network applies when the valid chain overtakes the invalid one corrected the history.
According to the postmortem, the NEAR Intents protocol processed an exchange of 11,000 LTC (approximately USD 605,000) for bitcoin (BTC) that was left unsupported after the reorganizationgenerating a significant loss for that platform. THORChain recorded a minor loss of 10 LTC under similar circumstances. Final dollar amounts are still being compiled by the Litecoin team.
What the postmortem admits went wrong
Burkett identified several structural flaws and exposed them in his article. MWEB validation was overly reliant on controls applied in the block construction process, but did not fully replicate them at the time of connecting a block to the chain, which is where the attacker managed to sneak in.
The March fix required a coordinated deployment exclusively among miners, with explicit instructions not to restart or rebuild chain history, which increased operational risk. Emergency coordination was improvised without formal channels or monitoring systems to detect chain forks, and several external services were not prepared to properly process a deep Litecoin reorganization, Burkett said.
However, the postmortem does not directly address the most uncomfortable criticism. As also reported by CriptoNoticias, researchers from the security group SEAL911 indicated that the March patch was applied privately almost a month before the second incidentwithout a massive alert to node operators to update.
That decision left a window where attackers could identify which nodes were still vulnerable and direct the DoS toward them. The Litecoin Foundation did not respond to that discrepancy between GitHub’s schedule and its official statements.
Finally, the network is currently operating on patch v0.21.5.4 and Burkett recommends upgrading immediately and verifying that the node is syncing correctly with that version.
