A malicious node would have leaked cryptographic keys to access THORChain vaults.
RUNE, THORChain’s native token, fell 18% in the last 24 hours.
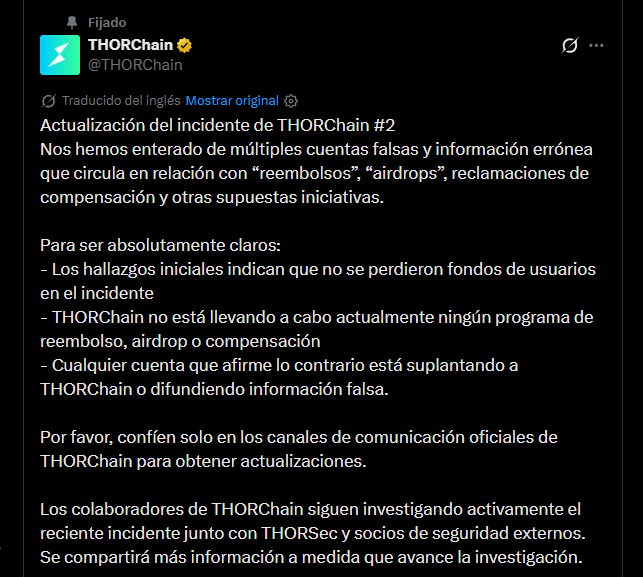
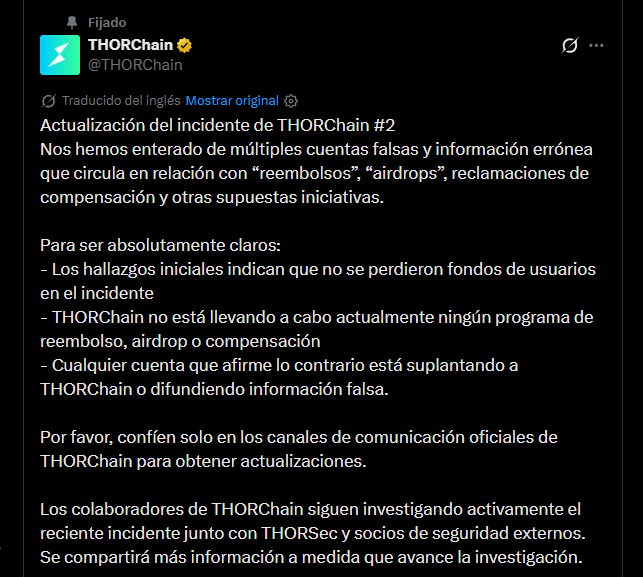
The THORChain decentralized protocol team indicated today, May 16, that “no user funds were lost” after the hack suffered yesterday, in which the platform suffered outflows of more than USD 10 million. In addition, they denied the existence of a refund program, airdrops and compensations in progress, and that the investigation continues together with analysts from the THORSec and Outrider Analytics groups.
From THORChain they warned about the circulation of fake accounts offering refundsfree token releases and non-existent compensation programs. “Any account that claims otherwise is impersonating THORChain or spreading disinformation,” says the statement, which recommends consulting exclusively the official channels of the protocol.
ZachXBT, the on-chain security researcher who warned about the exploit, estimated losses of more than $10 million, a figure that THORChain has neither officially confirmed nor denied.
How did the attack operate, according to the preliminary investigation?
According to a first statementissued on May 15, hours after the hack, the attack operated internally to the protocol according to the decentralized platform team. The exploit compromised the vaults where THORChain custody external assets (bitcoin, ether and other cryptoassets), collectively controlled by its validator nodes, without directly affecting users’ balances.
THORChain identified, as the main theory of the attack, a vulnerability in the GG20 TSS implementation, a cryptographic scheme that allows multiple nodes to jointly sign transactions without any one possessing the full key. In this protocol, that mechanism authorizes cross-chain asset movements and when the nodes reach the required signature threshold, the vault executes the transaction.
According to the statement, the vulnerability would have allowed key material from participating nodes to be gradually leaked. By accumulating enough leaked information, The attacker reconstructed the entire private key of the vault and executed unauthorized outbound transactions. From the protocol’s perspective, those transactions were cryptographically valid (because the key used to sign them was correct), which prevented automatic detection mechanisms from blocking them.
The statement links the attack to a node newly incorporated into the network, identified by the address thor16ucjv3v695mq283me7esh0wdhajjalengcn84q, through connections between the Ethereum addresses used to acquire RUNE (the protocol’s native token) and those that received the stolen funds. At the time of publishing this article, the price of RUNE fell 18% in the last 24 hours.


The global pause extended by the nodes on May 15 expired in the early hours of May 16, according to messages posted on the official Telegram channel. However, the operational status of the platform is not confirmed: Post-hack communications did not announce a formal reopening of operations, although the THORChain web interface appears active at the time of publication. The exchange and sensitive operations were still officially stopped according to the last release available.
