The Security Operations Center (SOC) of the Bybit exchange published a report on April 21 in which it warned of an active malware campaign for macOS that impersonated Claude Code, Anthropic’s artificial intelligence (AI) development tool, to steal credentials and crypto assets.
Bybit’s SOC team explained that malware targeted more than 250 cryptocurrency wallet extensions installed in browsers and various desktop applications.
The investigation also documented attempts to replace legitimate applications such as Ledger Live and Trezor Suite (the software interfaces used by these brands’ physical wallets) with counterfeit versions hosted on infrastructure controlled by the attackers.
Bybit detected the malicious infrastructure, deployed internal detection measures to protect its own users and shared the indicators of the attack with the community, which does not imply having taken control or neutralized the campaign, which could remain active.
How did the hackers operate?
According to the exchange team, the campaign It was initially detected on March 12 and mitigated the same daywith expanded technical disclosure in the report from yesterday
The attackers took advantage of the growing adoption of Claude Code among developers, which allows coding tasks to be delegated directly from the terminal, as a hook for the campaign. According to Bybit SOC analysis, the case reflects a broader trend of attacks targeting developers by spoofing popular AI tools.
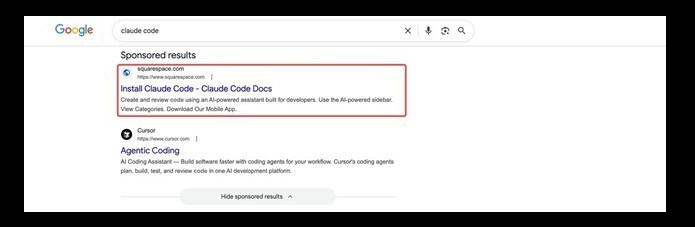
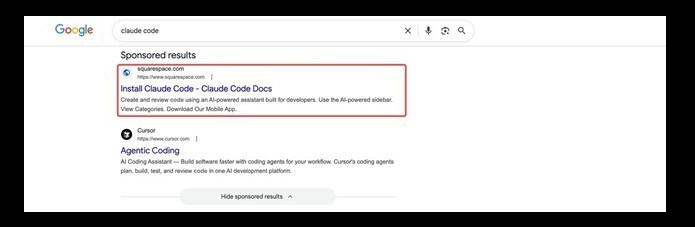
According to the report, the attackers used a technique called SEO poisoning (search results manipulation) to position a malicious domain at the top of Google when users searched for Claude Code.
Those who clicked were redirected to a fake page designed to imitate the tool’s legitimate documentation, from which a malicious installer was downloaded.
The malware operated in two stages. The first deployed an information theft program based on osascript, the macOS automation language.
Thus, hackers could extract browser credentials, macOS keychain entries (the system where the operating system stores passwords and access keys), active Telegram sessions, virtual private network (VPN) profiles and data from financial applications.
The second stage installed a backdoor written in the C++ language with advanced evasion capabilities, including scanning environment detection and remote command execution. According to Bybit’s research, that backdoor established persistence through system agents and allowed attackers to maintain continuous control over compromised devices.
The combination of stolen credentials, keychain data, and spoofed applications could give the attacker direct access to victims’ funds.
Bybit did not attribute the campaign to a specific hacker group and team, but did mention similarities with the AMOS and Banshee malware families, two malicious programs. Additionally, the document points out that Bybit’s SOC team achieved a 70% reduction in threat report generation times thanks to the use of AI.
A technique that other groups already use against the crypto ecosystem
The pattern described by Bybit aligns with that of “Mach-O Man”, the malware kit for macOS attributed to the Lazarus Group of North Korea, reported by CriptoNoticias this April 22.
Both campaigns aim to developers and executives of the cryptocurrency ecosystem on macOSan operating system historically perceived as more secure, and both steal keychain credentials, browser sessions, and wallet data.
The difference is the initial vector: “Mach-O Man” uses fake invitations to meetings on Telegram, while the campaign documented by Bybit used search result manipulation.
The common denominator is the displacement of the attack from the technical infrastructure towards social engineering aimed at people that operate that infrastructure.
